.svg)


Cyber Security

How SecQube aligns with the UK Cyber Security and Resilience Bill’s security and incident reporting requirements
Cyber Security

How Darkhub exposes the growing threat of hacking-for-hire services targeting crypto and communications
Talking AI

Choosing the right AI engine for cybersecurity: compliance, privacy and industry protection first
Cyber Security

Why cybersecurity teams should act like nightclub bouncers not Wall Street analysts
Talking AI

Why trust AI in cybersecurity: benefits versus valid safety concerns
Cyber Security
Understanding command and control incidents in Microsoft Sentinel environments
oAuth

Vercel breach exposes OAuth risks in AI tool integrations for cybersecurity leaders
Cyber Security

Optimising TI map IP entity rules in Microsoft Sentinel for faster threat detection
Cyber Security
Detecting and stopping beaconing attacks in Microsoft Sentinel environments
Cyber Security

How to prepare your Microsoft Defender environment against the RedSun privilege escalation exploit
Cybersecurity
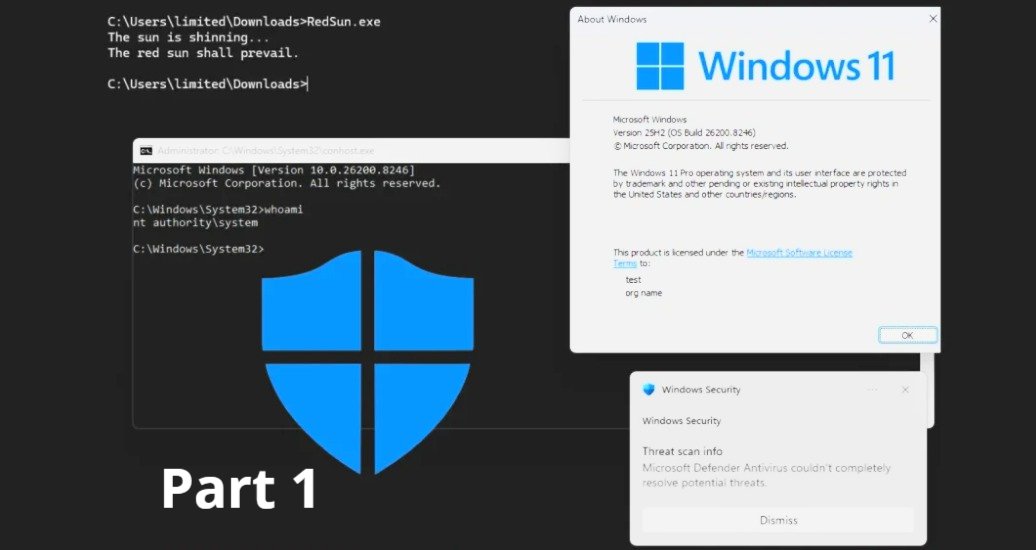
Technical steps to mitigate RedSun zero-day in Windows Defender for enterprise SOC teams
Sentinel Harvey AI

Splunk vs Microsoft Sentinel: Key differences for modern SOC leaders
Stealer Logs

VoidStealer infostealer bypasses Chrome ABE using debugger techniques
Cybersecurity

Who truly owns cybersecurity risk in the modern enterprise?
Cyber Security

How Cyber Essentials Plus v3.3 mandatory MFA rules challenge SMB cloud operations
Cyber Essentials

Preparing SMBs for Cyber Essentials Plus 2026 cloud scoping and access control shifts
Cyber Security

Cybersecurity risk assessment process: a practical workflow for assessing cyber risk factors
Cyber Security

Do Copilot agents leave a digital footprint in enterprise environments?
Cybersecurity
Comprehensive review of March 2026’s most disruptive ransomware and cyber attacks
Sentinel Harvey AI
How SecQube Harvey Portal and Microsoft Sentinel are revolutionising AI-driven SOC operations
Cyber Security

Hidden costs of scraping and transferring security data to external analysts
Cyber Security

Iranian hackers blurring lines between state espionage and ransomware in US critical infrastructure
Cyber Security

Is Palantir’s AI-powered defence technology secure against emerging cyber threats?
Cybersecurity

Why every modern organisation needs a robust security operations centre
Cyber Security

Mitigating Windows Error Reporting elevation of privilege vulnerabilities in enterprise environments
GSA
Why Entra Global Secure Access and Defender for Cloud Apps deliver unified Zero Trust security (Part-6)
SecQube

Boosting performance and compliance with Entra Global Secure Access deployment (Part-5)
VPN

Simplifying access policy management through Entra Global Secure Access integration (Part-4)
Cyber Security

Transitioning from VPNs to Entra Global Secure Access for hybrid workforces (Part-2)
Cyber Security

Why organisations should adopt Entra Global Secure Access for Zero Trust networks (Part-1)
Cyber Security

Best practices for patching multiple TP Link router command injection flaws in enterprise networks
Microsoft

Microsoft Authenticator CVE 2026 26123 explained for security teams
Cybersecurity

Why Behavioral Analytics Outsmarts AI-Driven Cyber Attackers
Talking AI

How C suite leaders can align AI strategy with core business outcomes
Cyber Security

Tanium Sentinel advisory collaboration accelerates threat investigations for enterprises
Cyber Security

Future of behavioral analytics against evolving AI cyber threats
Cyber Security
FBI warning on Russian phishing attacks targeting Signal users
Cyber Security

How Cohesity Sophos integration detects zero day threats in backups
Cyber Security

Overcoming MSSP blank canvas challenges with AI driven security automation
Healthcare

State sponsored AI malware exploits healthcare IoT in post war cyber onslaught
Cyber Security

CISA Chrome 0-day warning implications for enterprise browser security
Cyber Security

How AI driven defenses can proactively shield companies from evolving cyber threats
Cyber Security

Chrome extension malware risks in enterprise browser environments
Cyber Security

What is wiper malware and how it differs from ransomware threats
Cyber Security

How A0Backdoor malware evades detection in Microsoft Teams collaboration environments
Cyber Security
Copilot vs Foundry: which Microsoft AI platform fits your security operations roadmap?
Cyber Security

Apache ZooKeeper CVE-2026-24281: Reverse DNS fallback risks explained
Business

Navigating regulations with Claude Code Security compared to OpenAI Codex capabilities
Ben's Blog

In‑house SOC, outsourced SOC, or AI SOC platform: which model makes the most business sense?
Cyber Security

Inside the new wave of bogus GitHub tools pushing stealer malware
Cyber Security

Debunking the myth: why Linux faces just as many exploits as Windows
Business

Cost-effective threat hunting: optimising Sentinel workloads through smart automation
Cyber Security

From Lords amendment to Commons fight: Future of VPNs in UK
Cyber Security

Strategic defenses against AI agent hijacking like MS-Agent vulnerability (Part 2)
Cyber Security

MS-Agent Vulnerability CVE-2026-2256 Exposes AI Agents to Remote Hijacking Risks (Part One)
Bad Actors

Cyber Psychological Operations Targeting Civilian Apps During Iran Conflict
Cyber Security

Digital threats to India’s boom: 500m attacks, dark web war expands
Bad Actors

Security vulnerabilities in Claude Code exposing developer machines to hidden threats
Cyber Security

Detecting Dohdoor Backdoor DLL sideloading on Windows systems
Cyber Security

How Lazarus Group's Medusa ransomware shift threatens U.S. healthcare infrastructure
Cyber Security

Navigating security vulnerabilities in Claude Code for enterprise developers
Cyber Security

CVE-2026-27975 - Ajenti has a potential Remote Code Execution
Cyber Security

Infostealer economics: why DarkCloud is becoming a preferred threat for financially motivated attackers
Cyber Security

Is there a requirement for a simple to use multi-tenant Microsoft Sentinel solution?
Cyber Security

Achieving cost-effective security monitoring through Microsoft Sentinel's scalable model
Cyber Security

Can AI-driven automation bridge the cybersecurity skills gap effectively?
Cyber Security
.png)
Who watches the watchmen? Part 3: Oversight without blame
Cyber Security
.png)
Who watches the watchmen? Part 2: Dwell time is the real risk, not the breach
Cyber Security

How SecQube aligns with the UK Cyber Security and Resilience Bill’s security and incident reporting requirements
Cyber Security

How Darkhub exposes the growing threat of hacking-for-hire services targeting crypto and communications
Cyber Security

Why cybersecurity teams should act like nightclub bouncers not Wall Street analysts
Cyber Security
Understanding command and control incidents in Microsoft Sentinel environments
Cyber Security

Optimising TI map IP entity rules in Microsoft Sentinel for faster threat detection
Cyber Security
Detecting and stopping beaconing attacks in Microsoft Sentinel environments
Cyber Security

How to prepare your Microsoft Defender environment against the RedSun privilege escalation exploit
Cyber Security

How Cyber Essentials Plus v3.3 mandatory MFA rules challenge SMB cloud operations
Cyber Security

Cybersecurity risk assessment process: a practical workflow for assessing cyber risk factors
Cyber Security

Do Copilot agents leave a digital footprint in enterprise environments?
Cyber Security

Hidden costs of scraping and transferring security data to external analysts
Cyber Security

Iranian hackers blurring lines between state espionage and ransomware in US critical infrastructure
Cyber Security

Is Palantir’s AI-powered defence technology secure against emerging cyber threats?
Cyber Security

Mitigating Windows Error Reporting elevation of privilege vulnerabilities in enterprise environments
Cyber Security

Transitioning from VPNs to Entra Global Secure Access for hybrid workforces (Part-2)
Cyber Security

Why organisations should adopt Entra Global Secure Access for Zero Trust networks (Part-1)
Cyber Security

Best practices for patching multiple TP Link router command injection flaws in enterprise networks
Cyber Security

Tanium Sentinel advisory collaboration accelerates threat investigations for enterprises
Cyber Security
FBI warning on Russian phishing attacks targeting Signal users
Cyber Security

Future of behavioral analytics against evolving AI cyber threats
Cyber Security

How Cohesity Sophos integration detects zero day threats in backups
Cyber Security

Overcoming MSSP blank canvas challenges with AI driven security automation
Cyber Security

CISA Chrome 0-day warning implications for enterprise browser security
Cyber Security

How AI driven defenses can proactively shield companies from evolving cyber threats
Cyber Security

Chrome extension malware risks in enterprise browser environments
Cyber Security

What is wiper malware and how it differs from ransomware threats
Cyber Security

How A0Backdoor malware evades detection in Microsoft Teams collaboration environments
Cyber Security
Copilot vs Foundry: which Microsoft AI platform fits your security operations roadmap?
Cyber Security

Apache ZooKeeper CVE-2026-24281: Reverse DNS fallback risks explained
Cyber Security

Inside the new wave of bogus GitHub tools pushing stealer malware
Cyber Security

Debunking the myth: why Linux faces just as many exploits as Windows
Cyber Security

From Lords amendment to Commons fight: Future of VPNs in UK
Cyber Security

Strategic defenses against AI agent hijacking like MS-Agent vulnerability (Part 2)
Cyber Security

MS-Agent Vulnerability CVE-2026-2256 Exposes AI Agents to Remote Hijacking Risks (Part One)
Cyber Security

Digital threats to India’s boom: 500m attacks, dark web war expands
Cyber Security

Detecting Dohdoor Backdoor DLL sideloading on Windows systems
Cyber Security

How Lazarus Group's Medusa ransomware shift threatens U.S. healthcare infrastructure
Cyber Security

Navigating security vulnerabilities in Claude Code for enterprise developers
Cyber Security

CVE-2026-27975 - Ajenti has a potential Remote Code Execution
Cyber Security

Infostealer economics: why DarkCloud is becoming a preferred threat for financially motivated attackers
Cyber Security

Is there a requirement for a simple to use multi-tenant Microsoft Sentinel solution?
Cyber Security

Achieving cost-effective security monitoring through Microsoft Sentinel's scalable model
Cyber Security

Can AI-driven automation bridge the cybersecurity skills gap effectively?
Cyber Security
.png)
Who watches the watchmen? Part 2: Dwell time is the real risk, not the breach
Cyber Security
.png)
Who watches the watchmen? Part 3: Oversight without blame
Ben's Blog

In‑house SOC, outsourced SOC, or AI SOC platform: which model makes the most business sense?
.svg)


SaaS

Experts
AI SOC

SOC
Incident

Skills Gap
Try today

SaaS





.svg)







.png)
.png)










.png)



